Integrations
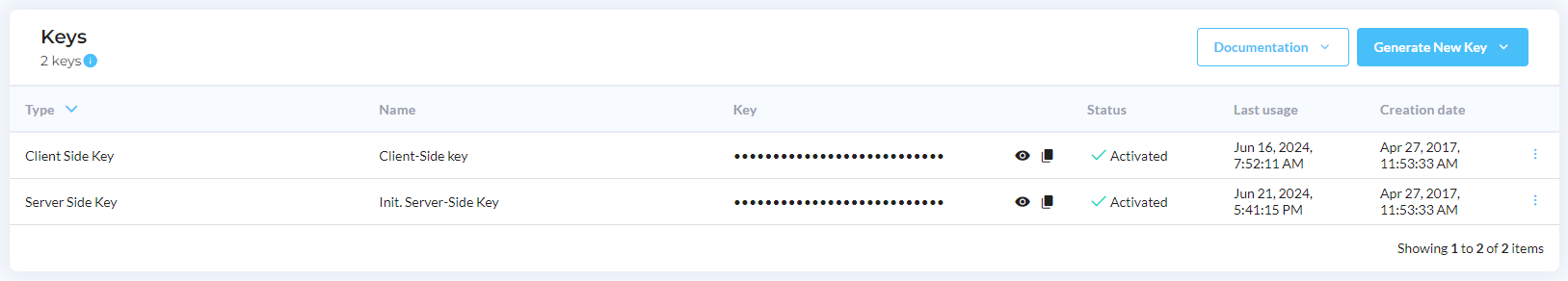
Keys
By default, DataDome provides two keys to authenticate your traffic. They are created during your onboarding.
- The server-side key required for any of our server-side integrations: this key must remain private and not be shared outside of your organization.
- The client-side key required our JavaScript Tag and mobile SDKs (iOSand Android): this key can be used publicly.
Key managementWe offer the ability to create, activate, deactivate and delete keys directly from the interface in your Dashboard. You can therefore perform a full key rotation if needed.
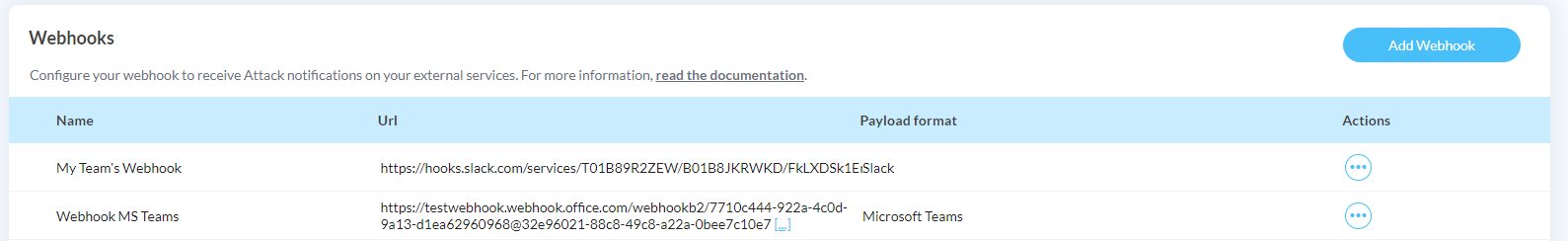
WebHooks
To be notified as soon as possible when your endpoints are under attack, you can use a DataDome Webhook to receive Attack Notifications in your existing third-party services.
You can find all steps required for all our supported integration in our dedicated section Webhook/Notification Integration]
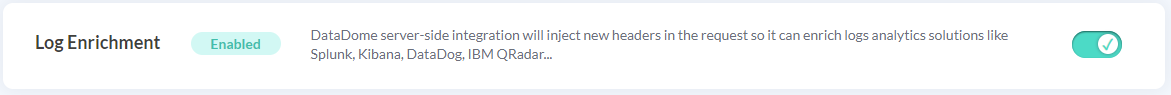
Log Enrichment
This feature is available for Corporate and Enterprise plans. Please reach DataDome team for more information.
If you want to enable the log enrichment to integrate them in your own tools, you could do it on this screen.
For more information about the integration, please visit Logs Integration.
First-Party JavaScript Tag
We recommend using a first-party setup to help ensure the JavaScript Tag runs on your protected pages if:
- The JavaScript Tag is blocked by ad blockers or privacy filters for many of your end users
- It makes it easier to integrate with existing CSP configurations by matching with existing rules
- The server-side integration is based on AWS CloudFront (due to limitations on response cookies)
The JavaScript Tag is an essential part of the bot protection process as it displays challenges, collects signals and helps with session management.
Using a First-Party JS Tag will reduce the risk of having the JS Tag blocked, which can impact the quality of the detection.
A First-Party JS Tag will be loaded as a first-party resource on a subdomain of yours that is configured as an alias of DataDome's domain and will avoid pulling the JS Tag from js.datadome.co.
Let's Encrypt CA compatibility awarenessYour CAA DNS record for the root domain of your First-Party JS Tag domain should allow Let's Encrypt to issue SSL certificates for your root domain.
You should be ok with using Let's Encrypt:
- Let's Encrypt only offers basic DV (Domain Validation) SSL certificates
- Let's Encrypt doesn't offer OVs (Organization Validation) and EVs (Extended Validation) SSL certificates
- Some platforms may have compatibility issues
- Geographic/political reasons may prevent Let's Encrypt from issuing an SSL Certificate for your First-Party JS Tag domain
This should be a non-issue in 99% of the cases, but if you're not sure with Let's Encrypt compatibility on your side you should ask your System Administrator.
Follow the 4 steps below in order to configure a First-Party JS Tag from the Integrations section of your dashboard.
1. Add a subdomain
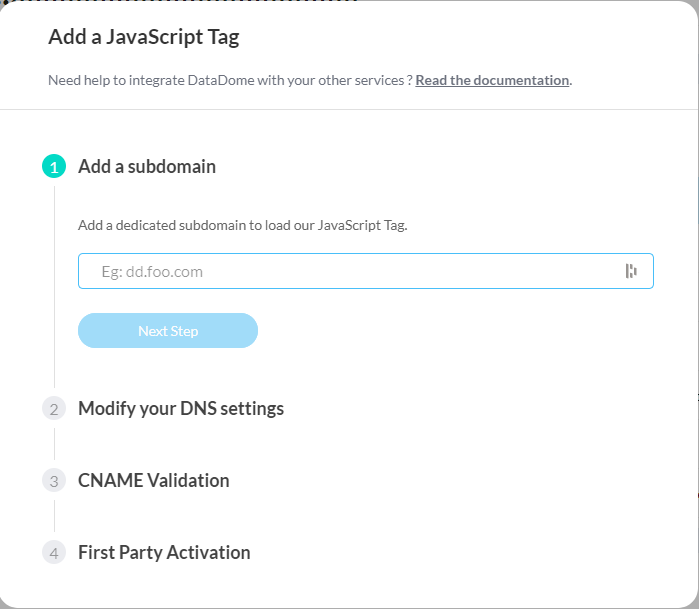
Enter a subdomain to use for a First-Party JS Tag setup
2. Modify your DNS settings
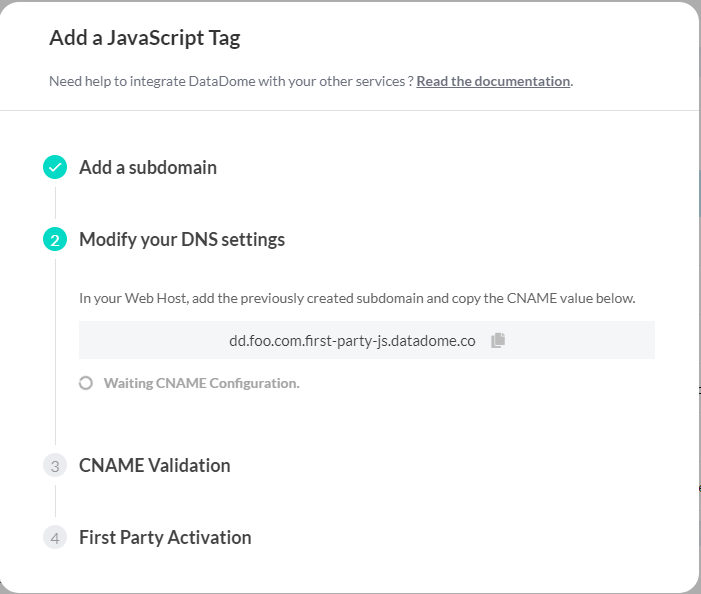
This step will wait for your CNAME validation, DataDome is notified automatically when it is done on your end
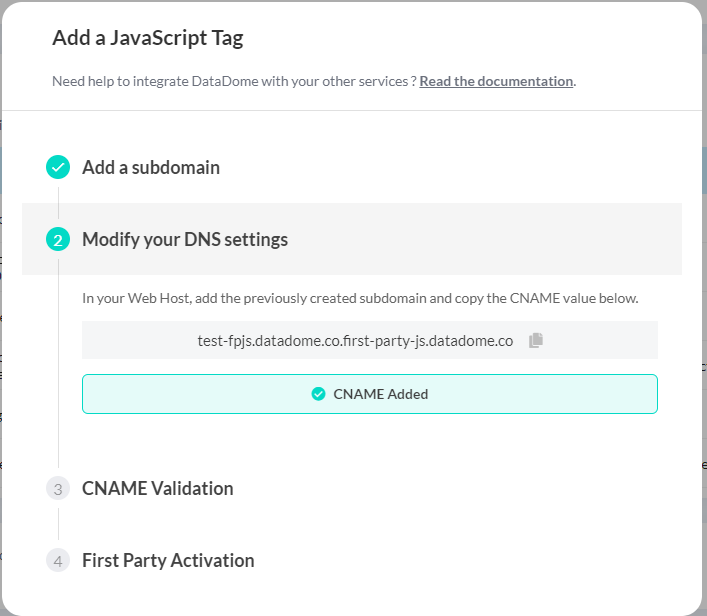
When DataDome detects that the CNAME has been added on your side
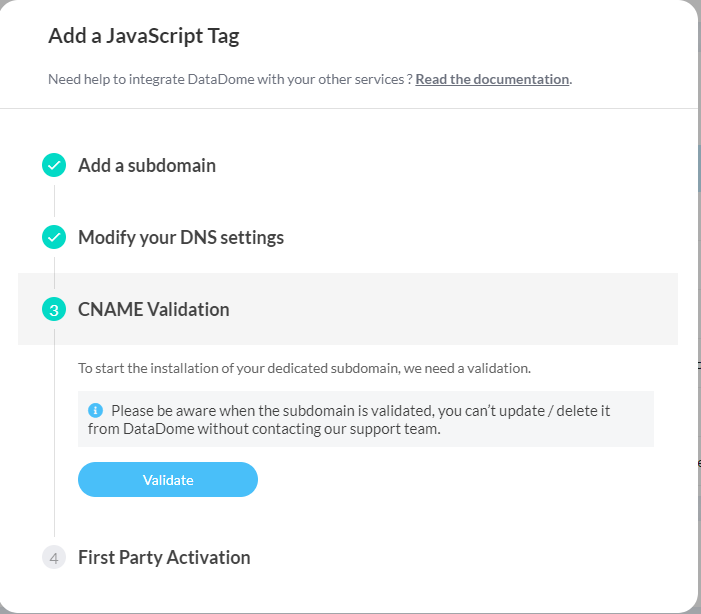
3. Validate the CNAME
4. Activate the first-party subdomain
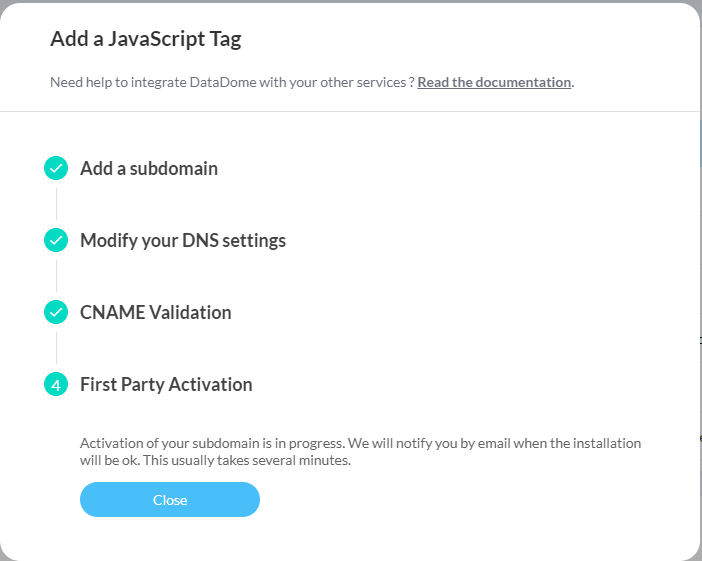
You'll receive a confirmation email when the activation is done
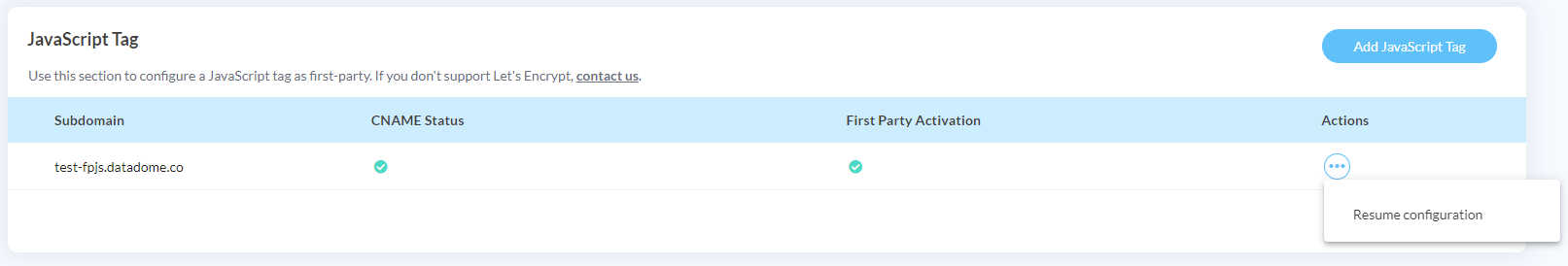
You can suspend and resume the configuration at any time
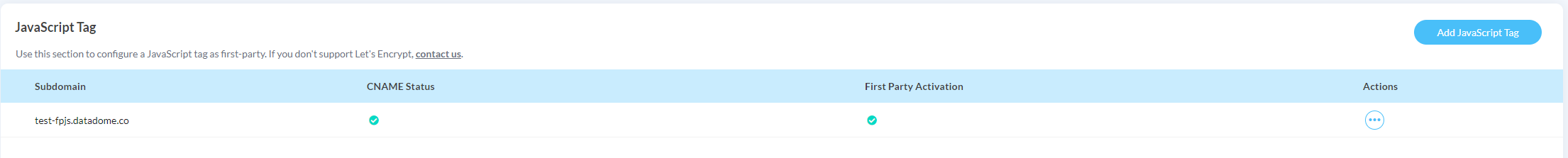
When closing the setup pop-in, you will see the status of the operation on the page.
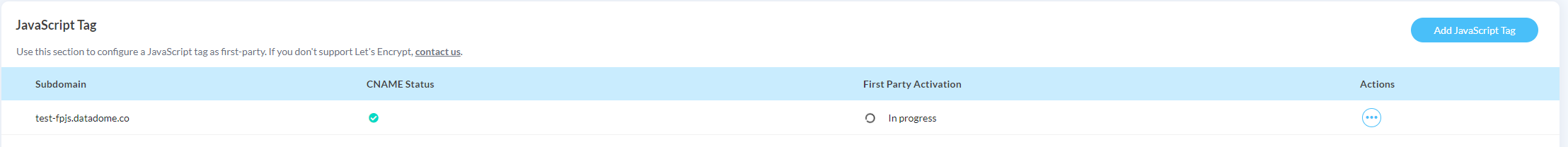
When the activation is completed, you will see a green checkmark on all statuses.
5. Update your JavaScript Tag loader
You need to update the JavaScript Tag loader to use the subdomain that was just created.
Replace SUBDOMAIN_FIRSTPARTY_JAVASCRIPT_TAG with your new subdomain in the src attribute of the <script> tag:
<script>
window.ddjskey = 'YOUR_DATADOME_JS_KEY';
window.ddoptions = {};
</script>
<script src="https://SUBDOMAIN_FIRSTPARTY_JAVASCRIPT_TAG/tags.js" async></script>Once deployed, the tags.js script will be delivered by your first-party subdomain from the /tags.js route and signals will be collected by our API through the /js/ route.
First-Party JS Tag deletionTo delete a First-Party JS Tag, please contact the support team.
Updated 2 months ago
