JavaScript Tag
Purpose
Installing the JavaScript Tag is required for two reasons:
- Guarantee an optimal level of detection, combined with any server-side integration from DataDome.
- Ensure that response pages are displayed when requests made with
XMLHttpRequestorFetchare blocked.
About thedatadomecookieOur JS Tag and response pages (e.g. Device Check challenges) require read and write access to the
datadomecookie to work as expected.For this reason, tampering with attributes of the cookie must be avoided, especially with
HttpOnly.More details about our cookies on this page.
Signals
The JavaScript Tag will provide our detection engine with more insights on the clients that are executing the script.
It collects behavioral data from the client (i.e. the web browser in most cases) such as mouse movements or key strokes. Generic information is also collected about the OS, the browser itself, the GPU, etc.
Many tests also run to verify the consistency of built-in functions and attributes linked to known bots, which enables DataDome to detect among other things:
- Headless Chrome
- Puppeteer
- Puppeteer Extra Stealth
- Selenium (even modified)
Privacy concernsThe JavaScript Tag's purpose is focused on bot detection and not tracking: the script doesn't collect information that may be considered as invasive of user privacy such as canvas fingerprinting. Therefore, the collected fingerprint doesn’t have a high entropy or uniqueness to it.
Installation
Prerequisites
- The client-side key available in your DataDome dashboard
Recommended integration (latest)
- Copy the code snippet below.
- Paste it at the start of the
<head>element. - Replace
YOUR_DATADOME_JS_KEYin the snippet with your actual client-side key.
<script>
window.ddjskey = 'YOUR_DATADOME_JS_KEY';
window.ddoptions = {
// Add your configuration here
};
</script>
<script src="https://js.datadome.co/tags.js" async></script>Your document should look like this:
<head>
<script>
window.ddjskey = 'YOUR_DATADOME_JS_KEY';
window.ddoptions = {
// Add your configuration here
};
</script>
<script src="https://js.datadome.co/tags.js" async></script>
<!-- Other head elements go here -->
</head>
<body>
<!-- Your website content goes here -->
</body>
On the importance of loading the JavaScript Tag earlyIt is highly recommended to load the JavaScript Tag first or as early as possible to ensure the following:
- Intercept protected requests (using
XMLHttpRequestorFetch) and guarantee the display of challenges- Preserve session continuity when using the
sessionByHeaderoption- Maintain valid referrer data for your client-side analytics after passing a challenge
⚠️ Install the JavaScript Tag directly in the HTML code. Do not use a Tag Manager.
Versioned integration
Starting with version 5.1.13, the JS Tag is available on versioned routes for users who require strict control over vendor scripts they are loading, e.g. for PCI DSS compliance.
Versioned routes are available as:
https://js.datadome.co/vX.Y.Z/tags.jshttps://<first_party_domain>/vX.Y.Z/tags.jsfor users of First-Party JS Tag integrations
ℹ️ Versioned routes are immutable.
Example of script URL to use with version 5.1.13:
<script src="https://js.datadome.co/v5.1.13/tags.js" async></script>With SRI (subresource integrity)
With the introduction of versioned routes comes the support of SRI (subresource integrity).
SHA256 hashes are available at:
https://js.datadome.co/vX.Y.Z/tags-checksum.sha256https://<first_party_domain>/vX.Y.Z/tags-checksum.sha256
ℹ️ The crossorigin attribute is also required, as per the documentation from MDN:
For subresource-integrity verification of a resource served from an origin other than the document in which it's embedded, browsers additionally check the resource using Cross-Origin Resource Sharing (CORS), to ensure the origin serving the resource allows it to be shared with the requesting origin.
Example of usage with version 5.1.13:
<script src="https://js.datadome.co/v5.1.13/tags.js"
integrity="sha256-HOIiRtvHWmf9qHMfJQo89Ldq8N9G8xQ1VHJyGzuhyY0="
crossorigin="anonymous"
async
>
</script>Configuration
Configuration guideℹ️ Find more details on how to configure the JavaScript Tag onthis page.
Content Security Policy (CSP)
In order to integrate the JavaScript Tag on a website that uses Content Security Policy (CSP), update the directives in your website's policy.
When do I need to update my CSP directives?You will only need to follow the instructions below if you use any of the listed directives, e.g.
script-src,frame-src, etc. or any of their fallbacks.For example: script-src has default-src as a fallback, so our recommendations for
script-srcwill have to be followed if one of them is defined.If you are not using one of them, you do not have to add it.
script-src and script-src-elem
script-src and script-src-elem
If you usescript-src-elemCSP 3 introduced script-src-elem as an alternative to script-src.
Instructions below are valid for both.
Two script-src or script-src-elem directives are required for the initial inline script and the <script> element that is added subsequently.
script-src nonce-2726c7f26cto allow a nonce-source instead of using theunsafe-inlinedirective2726c7f26chere is an example, do not use it as is: this part should be generated dynamically for each request to load a page with a CSP
script-src js.datadome.co ct.captcha-delivery.comjs.datadome.cowill allow the<script>element to load the JavaScript Tag from this domainct.captcha-delivery.comwill allow the scripts of our response pages to be loaded from this domain after a request has been blocked
Documentation about using a nonce-source for the inline script can be found on this page from MDN.
In practice, the nonce value should then be applied on the <script> element that contains our inline script described above and other inline scripts as well.
For example:
<script nonce="2726c7f26c">
window.ddjskey = 'YOUR_DATADOME_JS_KEY';
window.ddoptions = {
// Add your configuration here
};
</script>
<script src="https://js.datadome.co/tags.js" async></script>
connect-src
connect-srcconnect-src api-js.datadome.coto allow the JavaScript Tag to send the fingerprint back to our API
About First-Party JavaScript TagIf you are using a First-Party JavaScript Tag setup, you might need to replace
api-js.datadome.cowith the first-party domain that you are using, unless this domain is already covered by an existingconnect-srcdirective
frame-src
frame-srcframe-src *.captcha-delivery.comto allow our response pages to be loaded from an<iframe>element after a request has been blocked
worker-src
worker-srcworker-src blob:to allow loading our web worker to load from Blob URLs. This ensures the collection of specific fingerprints by the worker, helping to offload tasks from the main thread.
First-party setup
We recommend using a first-party setup to help ensure the JavaScript Tag runs on your protected pages if:
- The JavaScript Tag is blocked by ad blockers or privacy filters for many of your end users
- It makes it easier to integrate with existing CSP configurations by matching with existing rules
- The server-side integration is based on AWS CloudFront (due to limitations on response cookies)
The JavaScript Tag is an essential part of the bot protection process as it displays challenges, collects signals and helps with session management.
Using a First-Party JS Tag will reduce the risk of having the JS Tag blocked, which can impact the quality of the detection.
A First-Party JS Tag will be loaded as a first-party resource on a subdomain of yours that is configured as an alias of DataDome's domain and will avoid pulling the JS Tag from js.datadome.co.
Let's Encrypt CA compatibility awarenessYour CAA DNS record for the root domain of your First-Party JS Tag domain should allow Let's Encrypt to issue SSL certificates for your root domain.
You should be ok with using Let's Encrypt:
- Let's Encrypt only offers basic DV (Domain Validation) SSL certificates
- Let's Encrypt doesn't offer OVs (Organization Validation) and EVs (Extended Validation) SSL certificates
- Some platforms may have compatibility issues
- Geographic/political reasons may prevent Let's Encrypt from issuing an SSL Certificate for your First-Party JS Tag domain
This should be a non-issue in 99% of the cases, but if you're not sure with Let's Encrypt compatibility on your side you should ask your System Administrator.
Follow the 4 steps below in order to configure a First-Party JS Tag from the Integrations section of your dashboard.
1. Add a subdomain
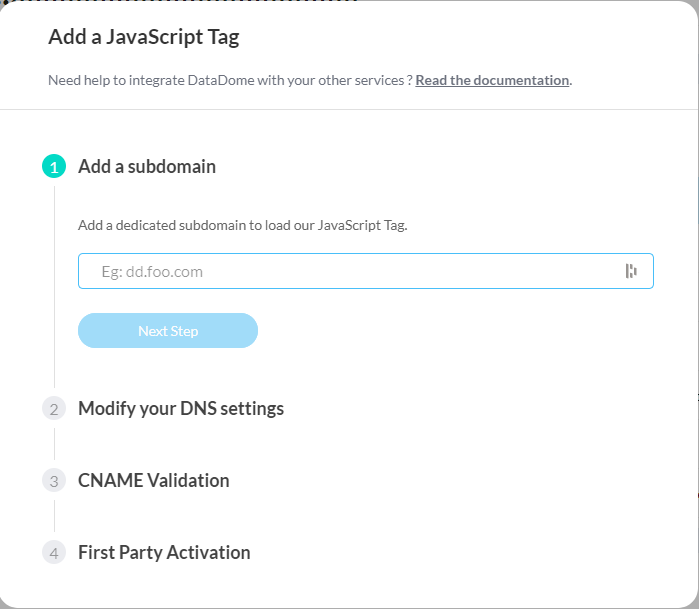
Enter a subdomain to use for a First-Party JS Tag setup
2. Modify your DNS settings
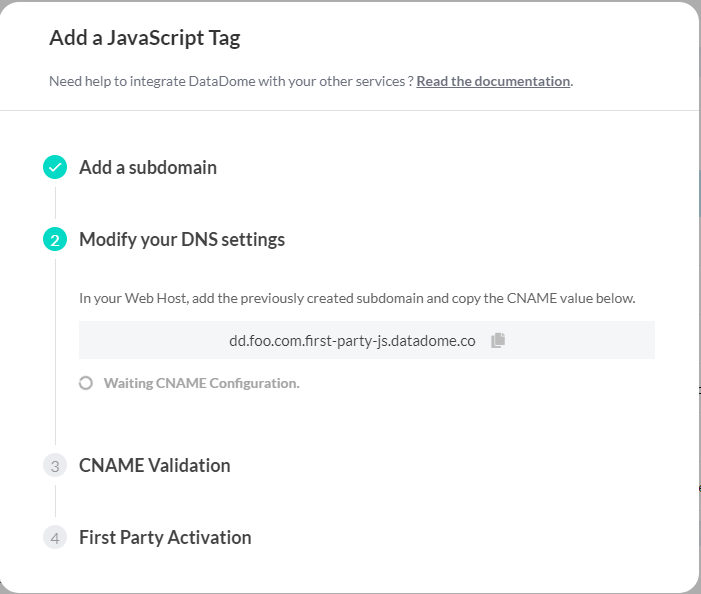
This step will wait for your CNAME validation, DataDome is notified automatically when it is done on your end
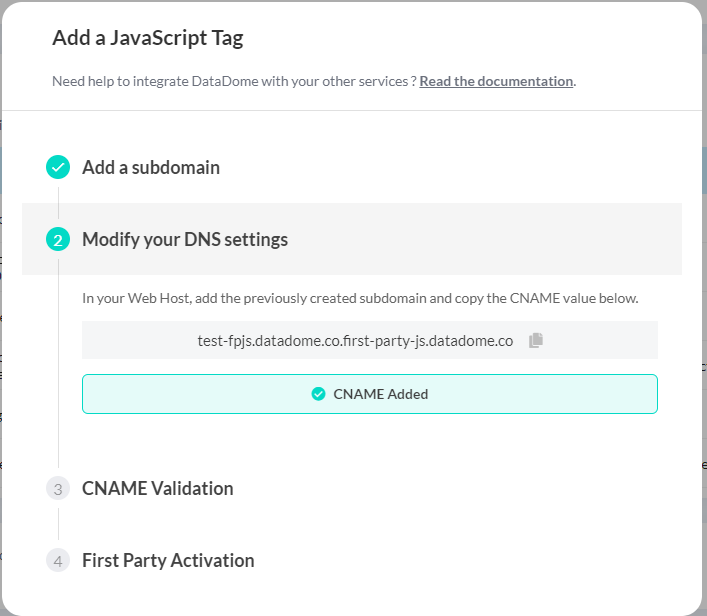
When DataDome detects that the CNAME has been added on your side
3. Validate the CNAME
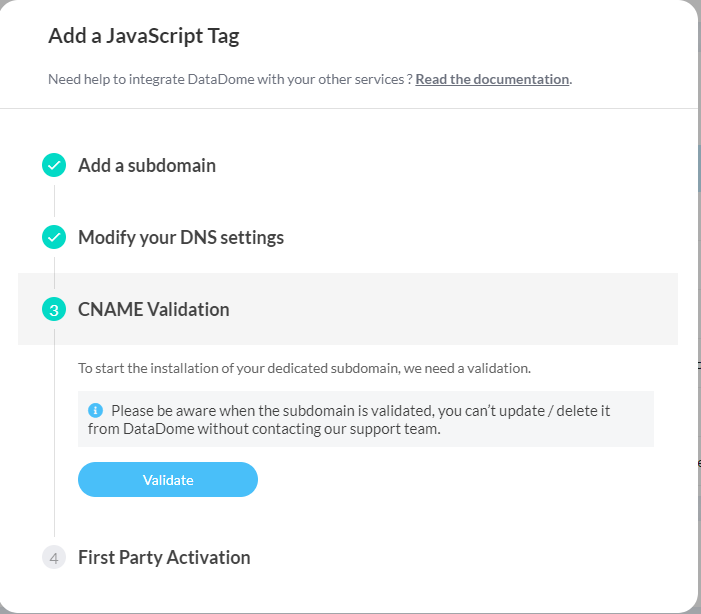
4. Activate the first-party subdomain
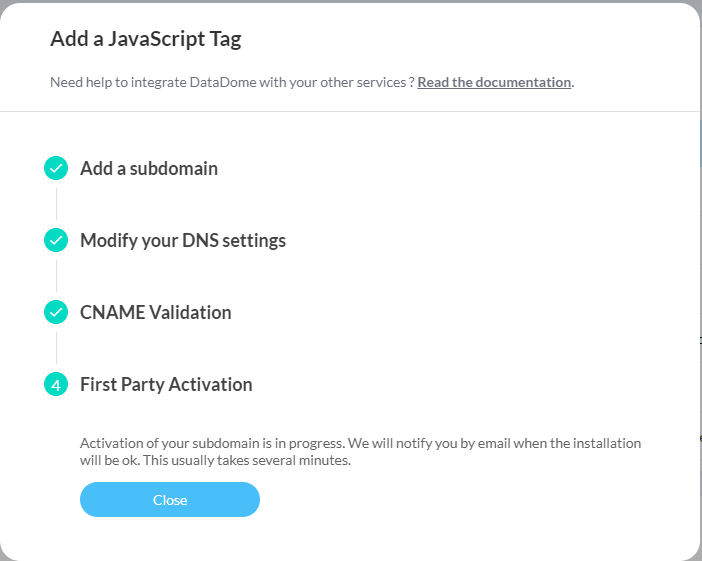
You'll receive a confirmation email when the activation is done
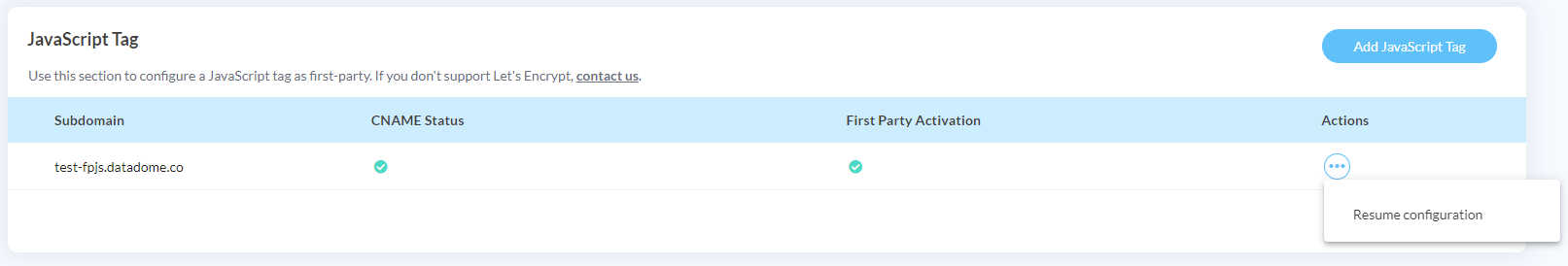
You can suspend and resume the configuration at any time
When closing the setup pop-in, you will see the status of the operation on the page.
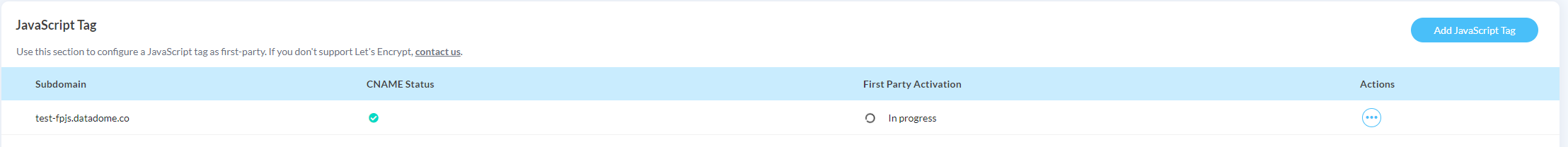
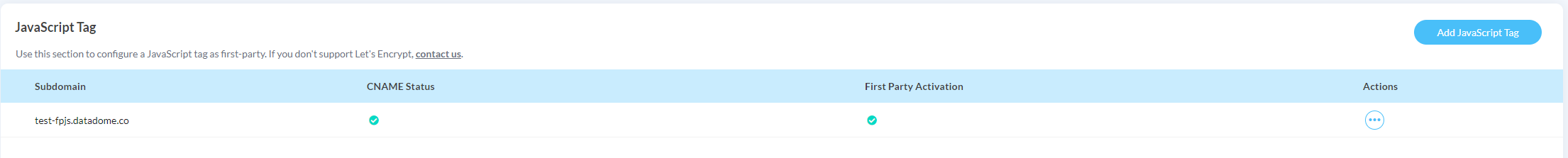
When the activation is completed, you will see a green checkmark on all statuses.
5. Update your JavaScript Tag loader
You need to update the JavaScript Tag loader to use the subdomain that was just created.
Replace SUBDOMAIN_FIRSTPARTY_JAVASCRIPT_TAG with your new subdomain in the src attribute of the <script> tag:
<script>
window.ddjskey = 'YOUR_DATADOME_JS_KEY';
window.ddoptions = {};
</script>
<script src="https://SUBDOMAIN_FIRSTPARTY_JAVASCRIPT_TAG/tags.js" async></script>Once deployed, the tags.js script will be delivered by your first-party subdomain from the /tags.js route and signals will be collected by our API through the /js/ route.
First-Party JS Tag deletionTo delete a First-Party JS Tag, please contact the support team.
First-party setup with your own reverse proxy
Why should I use this setup?
Faster page loadsServing both the JavaScript Tag and fingerprint endpoint from your own domain removes extra DNS lookups and TCP handshakes.
Bulletproof deliveryThird-party blockers such as ad blockers, privacy extensions or corporate firewalls can target unknown domains even if they are covered by first-party domains, by using CNAME uncloaking.
One-and-done setupIn case you have dozens of root domains, you configure your CDN and proxy once. No need to create a first-party CNAME for each of your root domains.
This is an alternative to a First-Party setup and you can reverse proxy our JavaScript Tag and API endpoint either through a CDN or a web server.
To have DataDome's JavaScript Tag on your own domains, you need to reverse proxy two components:
| Component | Public route | Origin |
|---|---|---|
| JavaScript Tag file (GET only) | example.com/tags.js | js.datadome.co/tags.js |
| Endpoint to forward fingerprints (POST only) | example.com/js/ | api-js.datadome.co/js/ |
When not defined, the endpoint value is automatically inferred by the JS Tag by using the /js/ route from the same origin (example above). If you want to use a different value, you need to update the JavaScript Tag configuration as described in the endpoint documentation.
Overriding theHostheaderYou need to override the
Hostheader withjs.datadome.coandapi-js.datadome.cowhen you are forwarding the request to DataDome's origin.Otherwise, DataDome origins will reject the request because the
Hostheader doesn’t match their domain.
Since the JavaScript Tag is being proxied, it will inherit DataDome’s default HTTP caching policy, and any new version will propagate through your proxy within minutes.
Configuration examples
# Global settings remain standard
global
log stdout format raw local0
# Define cache storage for /tags.js
cache datadome_javascript_tag_cache
total-max-size 10 # 10 MB cache storage
max-age 60 # Cache items for 60 seconds
defaults
mode http
timeout connect 5s
timeout client 30s
timeout server 30s
frontend http_in
bind *:80
# 1. Match requests for the DataDome JavaScript tag directly at root
acl is_tags_js path -i /tags.js
use_backend datadome_javascript_tag_backend if is_tags_js
# 2. Match requests to /js/ (POST requests for DataDome enrichment API)
acl is_datadome_js path_beg -i /js/
acl is_post method POST
use_backend datadome_javascript_fingerprint_backend if is_datadome_js is_post
backend datadome_javascript_tag_backend
server js_datadome js.datadome.co:443 ssl verify required ca-file @system-ca sni str(js.datadome.co)
http-request set-header Host js.datadome.co
http-response set-header Cache-Control "public, max-age=60"
http-request cache-use datadome_javascript_tag_cache # Serve from cache if available
http-response cache-store datadome_javascript_tag_cache # Store response in HAProxy cache
backend datadome_javascript_fingerprint_backend
server js_data_datadome api-js.datadome.co:443 ssl verify required ca-file @system-ca
http-request set-header Host api-js.datadome.co
option forwardfor # Forward original client IP in standard headerIn your CloudFront distribution:
- Create a new origin for `js.datadome.co`
- Create a behavior to match `/tags.js`
- Define `AllViewerExceptHostHeader` as the Origin Request Policy
(CloudFront overrides the Host header with the DataDome origin’s hostname)
- Create a new origin for `api-js.datadome.co`
- Create a behavior to match `/js/`
- Define `AllViewerExceptHostHeader` as the Origin Request Policy
(CloudFront overrides the Host header with the DataDome origin’s hostname)
Limitations:
CloudFront can’t route a request to a parent origin with a shorter base path.
For example, https://example.com/datadome/tags.js cannot be rewritten to fetch https://js.datadome.co/tags.js.
The client request's URL must be https://example.com/tags.js
http {
# ...
proxy_cache_path /var/cache/nginx/datadome keys_zone=datadome_cache:1m max_size=10m inactive=10m;
# ....
server {
# ....
# Match requests for the DataDome JavaScript tag
location = /tags.js {
proxy_pass https://js.datadome.co/tags.js;
proxy_ssl_server_name on; # Send the hostname from proxy_pass as SNI during SSL handshake
proxy_set_header Host js.datadome.co;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_cache datadome_cache; # Use the cache zone defined in http block
proxy_cache_valid 200 60s; # Cache successful responses for 60 seconds
}
# Match requests to /js/ (POST requests for DataDome enrichment API)
location /js/ {
proxy_pass https://api-js.datadome.co/js/;
proxy_ssl_server_name on;
proxy_set_header Host api-js.datadome.co;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}## Create a new host for /tags.js
- Adress: `js.datadome.co:443`
- Condition: `req.url.path == "/tags.js"`
- Override host: `js.datadome.co`
## Create a new host for /js/
- Adress: `api-js.datadome.co:443`
- Condition: `req.url.path == "/js/"`
- Override host: `api-js.datadome.co`
## Change the src of the JS Tag to use your domain
`<script src="https://your.domain/tags.js" async></script>`
// 1. Go to Cloudflare Dashboard → "Domains"
// 2. Select the domain used to proxy the JS Tag
// 3. Go to "Rules" → "Snippets" (https://blog.cloudflare.com/snippets/)
// 4. Click "Create Snippet"
// 5. Paste the code below and name the snippet
// 6. Click "Deploy", select "All incoming requests" and click "Done"
export default {
async fetch(request) {
const url = new URL(request.url);
// Proxy DataDome JS Tag
if (url.pathname === '/tags.js') {
return await fetch('https://js.datadome.co/tags.js');
}
// Proxy DataDome API endpoint
if (url.pathname === '/js/' && request.method === 'POST') {
return await fetch('https://api-js.datadome.co/js/', {
method: request.method,
headers: request.headers,
body: request.body
});
}
// Pass through all other requests
return await fetch(request);
},
};1. Access Bunny Dashboard, and click on the Pull-Zone you would like to update
2. Click on 'Edge Rules':
a. Click on '+ Add Edge Rule' button
b. Description: 'DataDome JavaScript Tag file'
c. Action:
'Override Origin URL',
Origin URL: 'https://js.datadome.co/tags.js'
d. Condition:
Set type to 'Match All'
'Request URL' > '*/tags.js'
'Request Method' > 'GET'
e. Click on 'Save Edge Rule' button
f. Go back to 'Edge Rules'
g. Click on '+ Add Edge Rule' button
h. Description: 'DataDome Endpoint to forward fingerprints'
i. Action:
'Override Origin URL',
Origin URL: 'https://api-js.datadome.co/js/'
j. Condition:
Set type to 'Match All'
'Request URL' > '*/js/*'
'Request Method' > 'POST'
k. Click on 'Save Edge Rule' button
3. Click on 'Scripting' under the Edge Platform menu item
4. Click on the DataDome middleware
5. Go to 'Variables' under the Environment menu item
6. Add the 'DATADOME_JS_URL' environment variable. The value should be YOUR-BUNNY-CDN-ENDPOINT/tags.js
7. Click on 'Save Variable'FAQ
Why am I seeing the JS Tag (tags.js) as the initiator of some requests?
tags.js) as the initiator of some requests?The JS Tag applies overrides on the XMLHttpRequest and Fetch APIs which may lead to its appearance in request initiator chains shown by developer tools.
This is required in order to apply some options (e.g. withCredentials) on requests sent with these APIs and intercept responses in case a challenge needs to be displayed and executed.
Can I self-host the DataDome JavaScript Tag?
While it is technically possible to self-host the JavaScript Tag, we strongly recommend using the reverse proxy setup instead. This approach keeps you automatically in sync with the latest version of the tag, ensures optimal detection quality, and requires no ongoing maintenance on your end.
If you still prefer to self-host the tag, please note that you are responsible for keeping your hosted version up to date. The JavaScript Tag must be refreshed within 7 days of a new version being released to avoid detection degradation. Falling out of sync with the latest version may impact the accuracy and effectiveness of bot protection.
Updated 23 days ago
